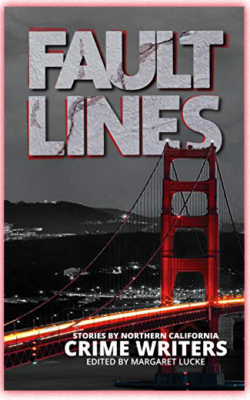
Fault Lines: Stories by Northern California Crime Writers
Available Now!
Available Now!
Fault lines in the earth can shake our world. Fault lines within people give rise to wrongs that must be righted. Sisters in Crime/Northern California’s first short story anthology invites you to take a journey into mystery and intrigue, with 19 short stories that explore crime, guilt, and justice in our earthquake-prone region and beyond.

Robin C. Stuart is a veteran cyber crime investigator and author. She consults on all things cyber security for Fortune 100 companies, authors, screenwriters, and media outlets. Her short story, SegFault, appears in Fault Lines: Stories by Northern California Crime Writers.